Amazon is a popular target for cyber criminals who want to exploit the trust and image of the company among its customers with emails. The vast majority of these emails pretend to be from Amazon in order to hack individual users and their Amazon accounts.
However, there is another, less known variant of phishing emails related to the company. This type of phishing email is not targeted at consumers, but rather at Amazon accounts. Amazon accounts are popular with cybercriminals because they can contain a wealth of identity. Compromised AWS accounts could also be exploited by hackers who have their own need for a reliable platform for computing services. Using such a platform free of charge for your own activities is definitely attractive.
AWS Accounts Are In Danger
A compromised AWS account gives attackers a variety of ways to commit cybercrime. Attackers who have control over an AWS account could potentially copy data from the account in order to use it for further attacks on customers, partners or clients. Request a ransom for the company’s data after it has been filtered from the account or after an organization has been banned from the account.
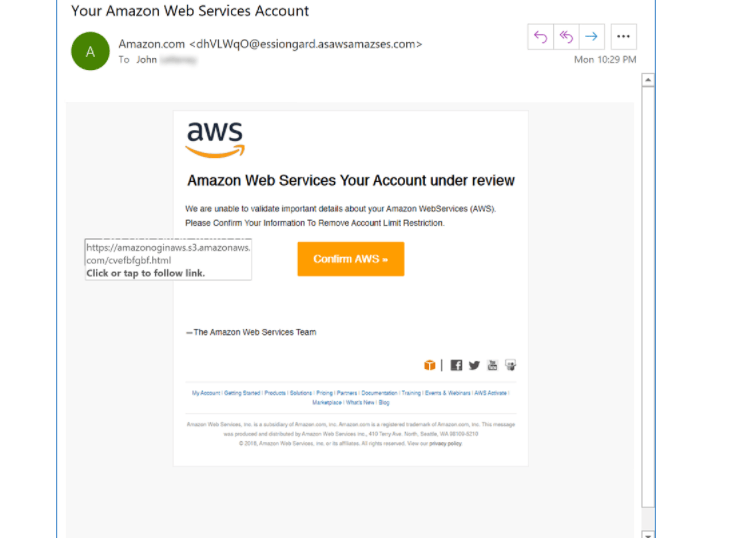
Of course, what could be done with a compromised AWS account depends on what those accounts are used for in the first place. Which data is stored in the account, how the account is configured and whether or not the account is used for public functions. The target for such phishing campaigns is usually cyber staff. In addition, executives within an organization are also potential victims of phishing emails related to AWS accounts – assuming they could forward AWS related email to the person who had access to the root user.
Unfortunately, it must be assumed that more and more cyber criminals will attack these types of accounts. The best defense is to train users with security training. Part of this training is to regularly test users with simulated attacks.
