The security researchers at Malwarebytes have uncovered a new web skimming attack in which users are cleverly lured onto the wrong track when they search online for graphic elements such as icons. Due to the imposed exit restrictions to protect against the spread of the coronavirus, cybercriminals have also recognized this. That’s why is credit card skimming and illegal tapping of information increased.
Credit Card Data Is The Main Mission
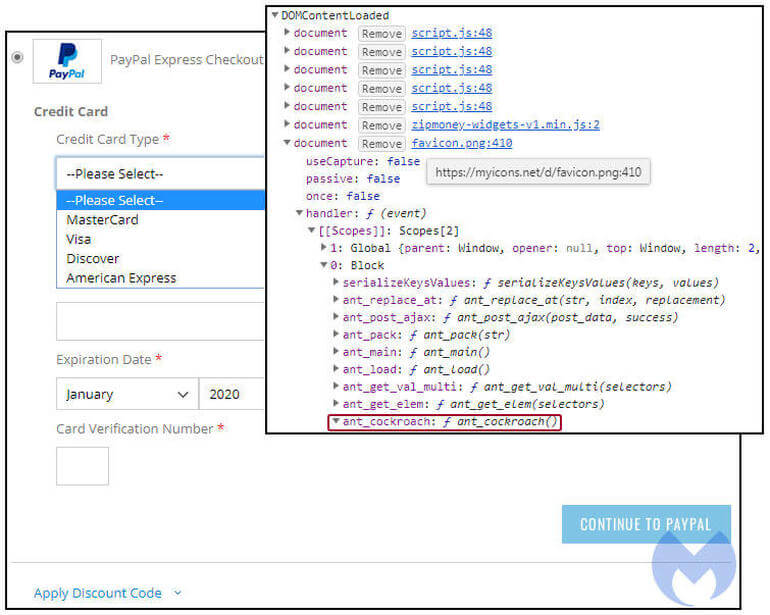
Cybercriminals registered a new website that visually resembles the domain and a well known database for icons and other graphic elements. Instead of providing useful icons for presentations, cybercriminals only use the fraudulent website for one purpose: to tap credit card data. Instead of providing a PNG image, the malicious server returns a JavaScript code that consists of a credit card payment form. This content is loaded dynamically into the document object model in order to overwrite the checkout option with its own dropdown menu.
Most Attacks Take Place On Monday
The study also found that criminals mainly focus on starting of the week. As a result, most attacks take place on Monday and decrease over the weekend. The United States and Canada have seen the most skimming attacks. The security researchers also assume that web skimming activities will continue to increase in the coming months.
The Security Researchers At Malwarebytes Provide The Following Security Tips
- Only rarely enter credit card details manually. Saving the payment data is recommended.
- Check the security seal. Unfortunately, they can be deceiving. When a website displays a corresponding logo, it does not always have to mean that this page is actually secure.
- Examine source code. This tip is more for tech save users. They can, examine the source code of a website with the help of developer tools, which as a side effect can switch off a skimmer that notices that it is being checked.
