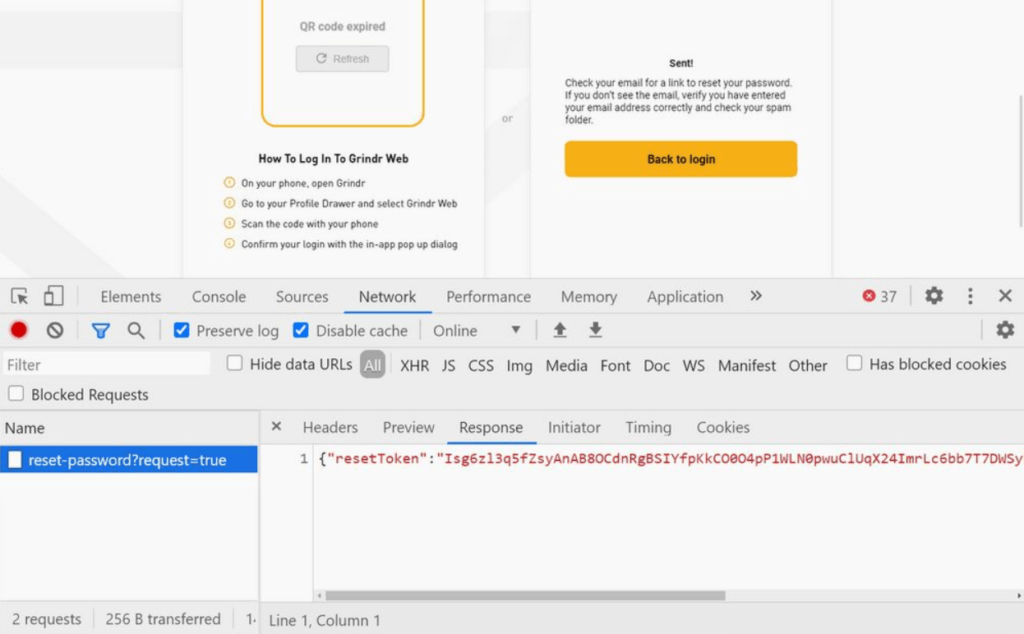
The Grindr account had a serious security gap. A hacker could completely take over an account using the feature to reset the password. On the website on which you requested to reset the password, you could read out the crucial data for the reset link and thus gain access to an account. Only an email of a Grindr user had to be hacked.
To reset a password, Grindr uses the common way with a reset option, which is sent to a users email upon request. Security researchers of the platform found out, that the website for requesting such a reset erroneously reveals the token that is actually intended to be part of the link, which in turn may only be made known to the requesting user. Since a reset from Grindr is always structured in the same way, the token can simply be encrypted into a link created by yourself. If a hacker has knowledge of an email that is stored in a Grindr account, a reset could be generated in this way. The hacker could already take over the entire user account.
Grindr Wants To Team Up With A Security Company
The security gap is closed and it is assumed that no hacker has exploited the gap. The company now wants to team up with a security firm and work to ensure that such vulnerabilities can be better communicated in the future. In addition, they want to offer a reward for finding further weak points.
Contact Was Only Established After A Tweet
Experts found out that a public tweet asked if anyone had any contact with the team at Grindr. Only then was contact made. The problem was then resolved relatively quickly. Affected users could also notice such an attack, as they would receive a reset email and would then no longer be able to log in with their password. People who use Grindr and have recently received an unexpected reset email should check as soon as possible that their password is still working. As Grindr’s chief operating officer Rick Marini told;