A Korean hacking group known as Higaisa is behind the recent spree of attacks against organizations that utilize the Zeplin collaboration platform.
These hacks carried out in a streak over the past few weeks via malicious short cut files (LNK).
Malware released an analysis of the threats. The analysis reads, “in this latest incident, Higaisa used a malicious shortcut file ultimately responsible for creating a multi-stage attack that consists of several malicious scripts, payloads and decoy PDF documents”. The analysis also reports details like the Indicators of Compromise (IoCs).
Higaisa, assumed to be a nation-state group, has presumably been in existence as far back as 2016; but publicly reared its head in 2019. The group attacks with artillery, which consist of typical RAT like Gh0st, PlugX, etc.
Victims of this group include government officials and human rights organizations.
The spree of attacks dates back to May 11th. Experts employed archive files: Project link and New copyright policy.rar” and “CV_Colliers.rar” to pinpoint the dual variants of the attacks that took place between the 12th and 31st of May respectively. Project link and New copyright policy.rar linked to attacks carried out against firms that utilize zeplin.io as hackers dispersed the LNK file via spear-phishing messages. Once access to the LNK file is possible, programmed orders are automatically carried out.
These were later presented to VirusTotal on May 12th. Victims started receiving the malicious RAR file on May 11th; giving credence to the fact that the LNK files were developed earlier that month.
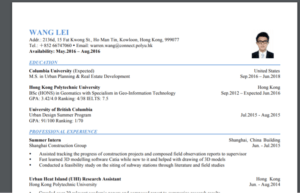
On May 30th, a false curriculum vitae (CV) of a Korean student, Wang Lei, was used as another form of weapon.
After observing all attacks, Malwarebytes noticed a similarity between the attacks and those reported by Anomali in March; which was COVID-19 related.
Higaisa M.O has been revealed to flow with the trend. They have taken advantage of the COVID-19 pandemic and exploited victims working from home; by mimicking the services needed to function remotely.
Prevailion’s researchers had this to say, “by analyzing individual elements of this campaign; we noted a number of correlations to prior threat actor reporting. […] Based upon the totality of available information, we assess with high confidence that this campaign was performed by the same actors responsible for the Coronavirus, Covid-19, themed campaign in March.”
Based on Google trends, three countries; India, United Kingdom, and the United States have been revealed to have an interest in the Zeplin app. This could serve as a clue to which “body” will be attacked next.
