Another day, another data breach by “db8151dd”.
Security researcher Troy Hunt has revealed details of the huge open Elasticsearch database he found online. Nicknamed db8151dd; the database contains unique details for approximately 22 million people, including their name, email address, phone number, real address, social media profile, and title.
HaveIBeenPwned fame Troy Hunt claimed he had discovered the db8151dd database in February. Hunt reveals that the database contains approximately 90GB of data and that the collection of information is on its own, rather than breaching public sites like many similar incidents in the past.
For example, Hunt reveals that including phone numbers are rare in such databases, but phone numbers are available in this case. He also noted that they strategically place personal files alongside people with whom they have interacted in the past. Surprisingly, it appears that the database has recognized the link between the two people.
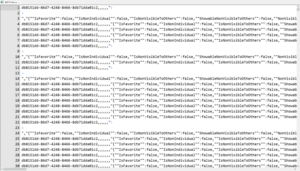
Screenshot of “db8151dd” data shared by Hunt.
In conclusion, the database can come from or establish contact with the customer relationship management system. According to his blog article, Hunt conducted a three-month investigation and obtained only three leads. These are the following three sentences that repeatedly appear in the data:
“This contact information is synced from Exchange. If you want to change the contact information, open OWA, and make the changes here.”
“Export from Microsoft Outlook (do not delete).”
“A contact created by Evercontact. (Evercontact is a contact management application available on Android)”.
Hunt Tweeted about the breach

However, on May 15, Covve, a Cyprus-based contact management solutions company, acknowledged the violation. Hunter also confirmed the identification of the source of the violation as the Covve Contacts app. This also explains the strategic location of the data because Covve uses an AI (artificial intelligence), compliant contact manager.
“On Friday the 15th, we learned of security incidents on the platform. Our team immediately began an investigation to determine the source and nature of the incident. A third party corrupted user data”. The company said that “our old system has been taken out of service.”
