Suspected state criminals have succeeded in compromising SolarWinds and smuggled a malware into updates. SolarWinds sells system security products used by more than 300,000 customers worldwide. These include many important companies and government authorities.
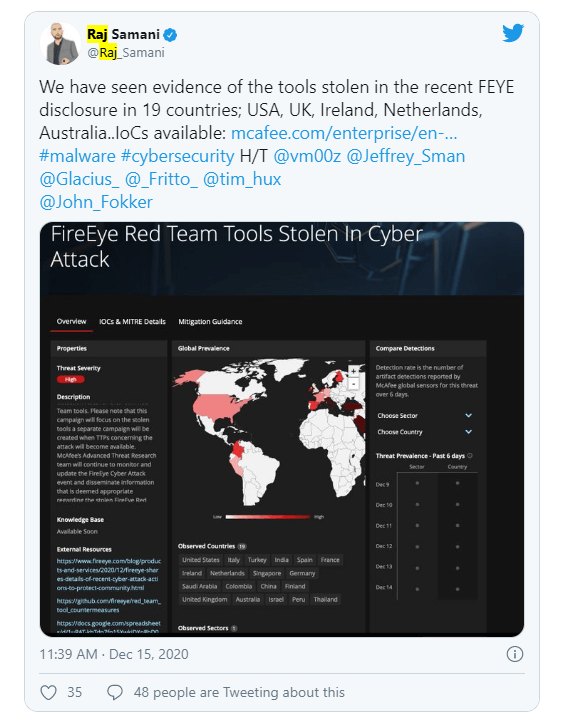
In recent months, cyber attackers have apparently been able to successfully break into several departments and and pull documents from the victims IT networks. In addition, there are indications that they were able to infiltrate Microsoft operations and read the victims mail undetected for months. It appears to be the same hackers that were responsible for the cyber activity on the security company FireEye.
Meanwhile, FireEye has discovered that there has been a supply chain attack on the platform. The hackers succeeded in smuggling a Trojan called into an update, which SolarWinds then distributed for the business software. How the hackers got into the system and hacked the Orion platform is still unclear.
The Trojan that was smuggled, acts like a backdoor on affected networks that can connect to servers, execute documents and exchange information. It is also possible to end network servers or restart them. The malware uses block lists to get tools running as processes, providers and drivers. In this way, the hackers managed to remain undetected in the networks for months.
The gateway is always the sunburst malware with which the company was hacked with updates. After an initial dormant period of up to two weeks, the malware gets commands from the servers and begins to investigate the compromised network. Microsoft also records the current state of knowledge in a post. Administrators of hacked customers can find data on security issues relating to the attack in the customer guide published by Microsoft on the latest state supported hacker attacks.
