A computer science student discovered some memory errors in Bitdefender’s software. Most of them should be easy to use to inject and execute your own code. It then runs with the rights of the software on the computer concerned. If you exploit these security gaps, you can bring a network completely under your control. All of the bugs are not really hard to find gaps, but rather for security researchers, like those that can easily be found. Almost half caused the lack of the important length in memory systems.
The Software As A Security Risk
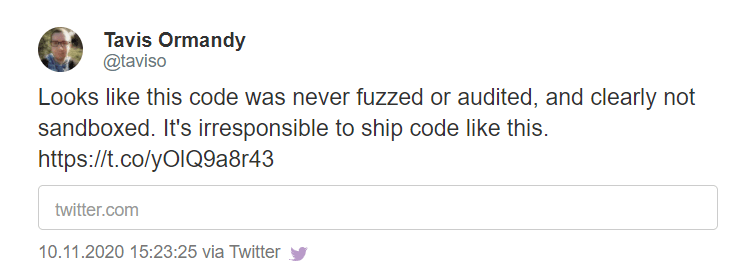
The main problem is that AV software has to unpack countless file documents. In many cases, the code from simple tools, such as an open unpacker, is simply used. The student was able to trace many of the gaps he discovered back to the tools. But they were not written for the highest security requirements. But that is exactly what a software does: not on the command line, but in the background, it unpacks every suspicious data that passes it. And in the case of Bitdefender, without additional shielding. A hacker only has to push his exploit roughly in the direction of his victim. Tavis Ormandy, who has identified several such loopholes in AV software himself, promptly comments that it is “irresponsible to deliver code like this”.
Security After Several Attempts
Not a glory either: Bitdefender often needed several attempts to properly close the security vulnerabilities. In one case, it didn’t work until the fourth patch. After all, these security gaps in Bitdefender have all been fixed since the beginning of November. It starts all over again when someone starts the next function for an obscure file. Bitdefender has meanwhile confirmed that the vulnerabilities could possibly be exploited. However, that would not be as easy as shown. In addition, they would like to thank the safety researcher who helped make the products safer.
