Many users see PDF document as a supposedly secure data exchange format for invoices, contracts and forms compared to office suites with their macro viruses and other exploits. Security researchers dealed with the PDF standard as part of Black Hat 2020 and found numerous implementation problems of the sometimes ambiguous standard as well as security traps in daily use.
PDF Files Make The Computer Unusable
For this purpose, some experts manipulated PDF documents on social media platforms like Twitter with an editor. The result: it can use simple endless loops, which increase the CPU load when opening or that are just a few bytes long and are embedded in the PDF, but which take up several gigabytes after opening.
To get to user passwords, hackers use a network share as a file path, which they start as a print job. This allows them to steal the user name in order to transport it to any URL on the internet via a URL backchannel. This means that login data can also be stolen with a prepared PDF document. The hash only needs to be cracked using known methods. And if the victim uses a VPN or a cloud package, the attacker can also use it to log into the company’s infrastructure in many cases.
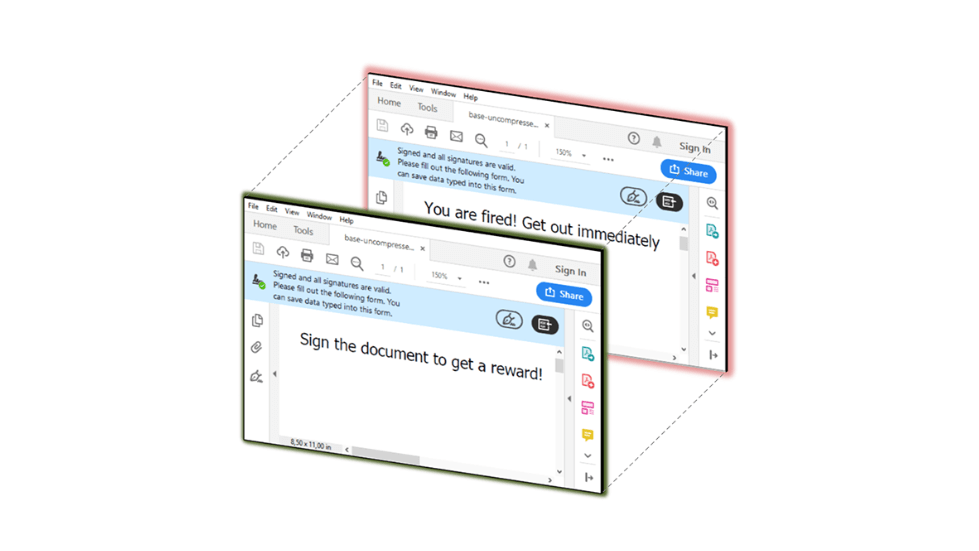
In addition, a hacker can use PDF documents to manipulate any file that the user has write access to. Experts also found an option for remote code execution with which an attacker can execute any code smuggled in the PDF on the target system. It regards all attacks that require user interaction as having failed: Often, a preview in the file manager is sufficient to carry out the attack. You can check whether your PDF reader is vulnerable to Shadow Attacks and update if necessary.
