A group of hackers took Apple rights and were responsible for many Apple security vulnerabilities over a period of three months. The security researchers have their work entitled. Cyber groups hacked Apple for 3 months.
One of the security gaps that was uncovered made it possible to use fake mails to access the iCloud of those hacked. This also means access to data such as private photos, emails and contacts.
Apple’s Quick response In This Case Is Widely Recognized
If the security vulnerabilities had been exploited by an attacker, Apple would have had to contend with massive disclosure and a loss of integrity. Precisely such independent inspections are also seen as important for the safety of products. The purpose of offering appropriate rewards is to create incentives for this, and in this case the whole thing probably worked very well. However, Apple only introduced its bounty program a few years ago and under public pressure.
A particularly serious security gap was in Apple’s mail box too. If the victim opened a prepared mail, the security researchers could carry out a cross site attack and read the personal data of the person concerned from the cloud. The security researchers show their attack in a proof of concept video. On top of that, the mail with the malicious code could be sent to all contacts stored in the account and spread like a virus.
55 Security Gaps
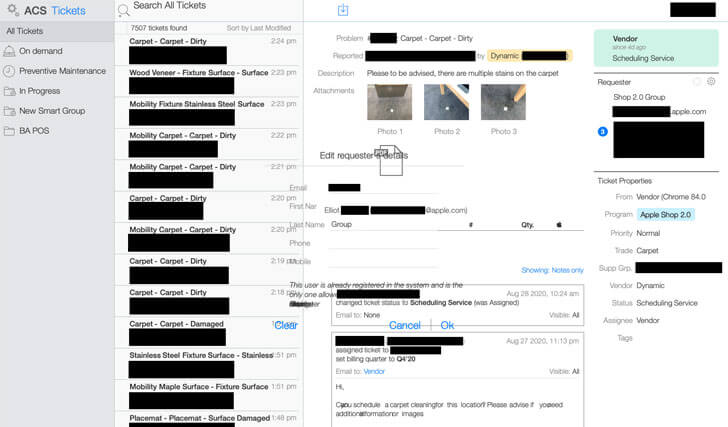
The researchers discovered another gap in Apple’s educators program. If teachers applied with a form on the site and entered their username, Apple assigned them the password. With this access data, third parties could then log in and hack the function. These security gaps are part of a list that made it possible, to access internal source and other resources, which can be used to track customer and employee problems.
